The potential drone vulnerability lies in an unencrypted downlink between the unmanned craft and ground control. The U.S. government has known about the flaw since the U.S. campaign in Bosnia in the 1990s, current and former officials said. But the Pentagon assumed local adversaries wouldn’t know how to exploit it, the officials said.
via ATTACKERMAN » Drone Hack? $26. American Arrogance? Priceless.
If it’s computerized, there is a hack for it. The fact that the Pentagon assumed that the locals wouldn’t be able to figure that out or rather decided that’s a fair explanation for the down link hack is ridiculous. We can’t just buy a new fangled gadget from a defense contractor to solve our problems. We need to be able to improve our own tech, and I’m not sure if it is really being done. Is there a way the Pentagon can hack the drones 10 output video feeds with noise (various dummy feeds) to throw off eavesdroppers before we are able to install feed encryption?
The WSJ article Ackerman sourced also details how the U.S. accuses Iran of supporting the dissemination of this hack. So what. We know Iran wants to support Shiite opposition forces in Iraq. Another Pentagon PR gem:
U.S. officials say there is no evidence that militants were able to take control of the drones or otherwise interfere with their flights. Still, the intercepts could give America’s enemies battlefield advantages by removing the element of surprise from certain missions and making it easier for insurgents to determine which roads and buildings are under U.S. surveillance.
The drone intercepts mark the emergence of a shadow cyber war within the U.S.-led conflicts overseas.
This illuminates two kinds of hacks. The “Cyber war” has always been here. Remember the Navajo Code Talker Marines? That was a hack we used in WW II. A good proactive hack.
Today, in Iraq, when IEDs were shredding vehicles, our soldiers were forced to hack their transports by up-armoring them with whatever metal they could find and armor paid for by their families back home. This is not a good hack, we are being out hacked. On top of that, we didn’t secure Iraq Army munitions at the beginning of the occupation, most of them walked away and are being rigged into this ever deadly, decades old hack that we can’t neutralize.
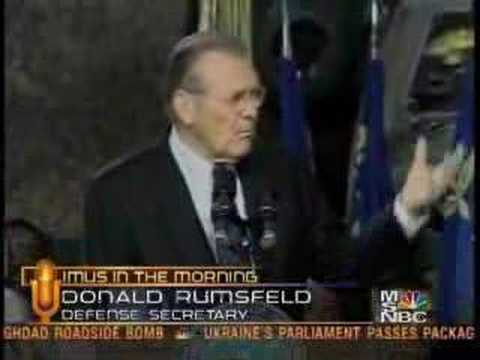
Either way, this is how wars are lost. Adversaries will find ways to neutralize our seemingly boundless power and funding for armed conflict with hacks. If we don’t evolve our war machinery, there will be hacks for them faster them faster than we can counter-hack. This is how war works, but this arrogance or tech malpractice is remnants of Rumsfeld’s Doctrine of “you go to war with the army you have, not the army you might want”. Heck of a job.